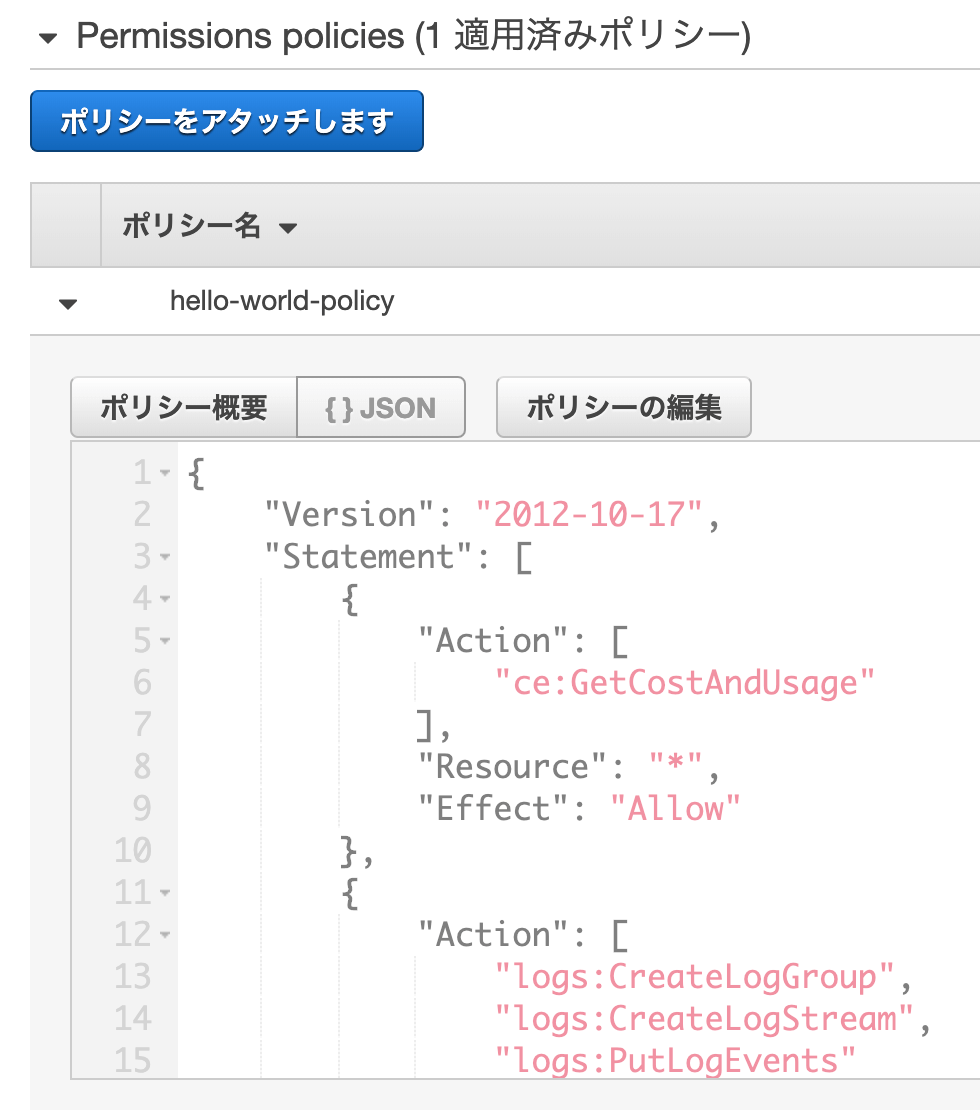
AWS IAM Introduction. An overview of AWS identity and access… | by Evan Kozliner | Towards Data Science

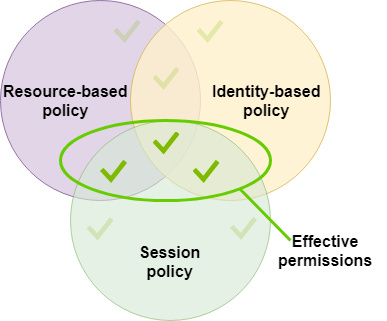
How to use resource-based policies in the AWS Secrets Manager console to securely access secrets across AWS accounts | AWS Security Blog
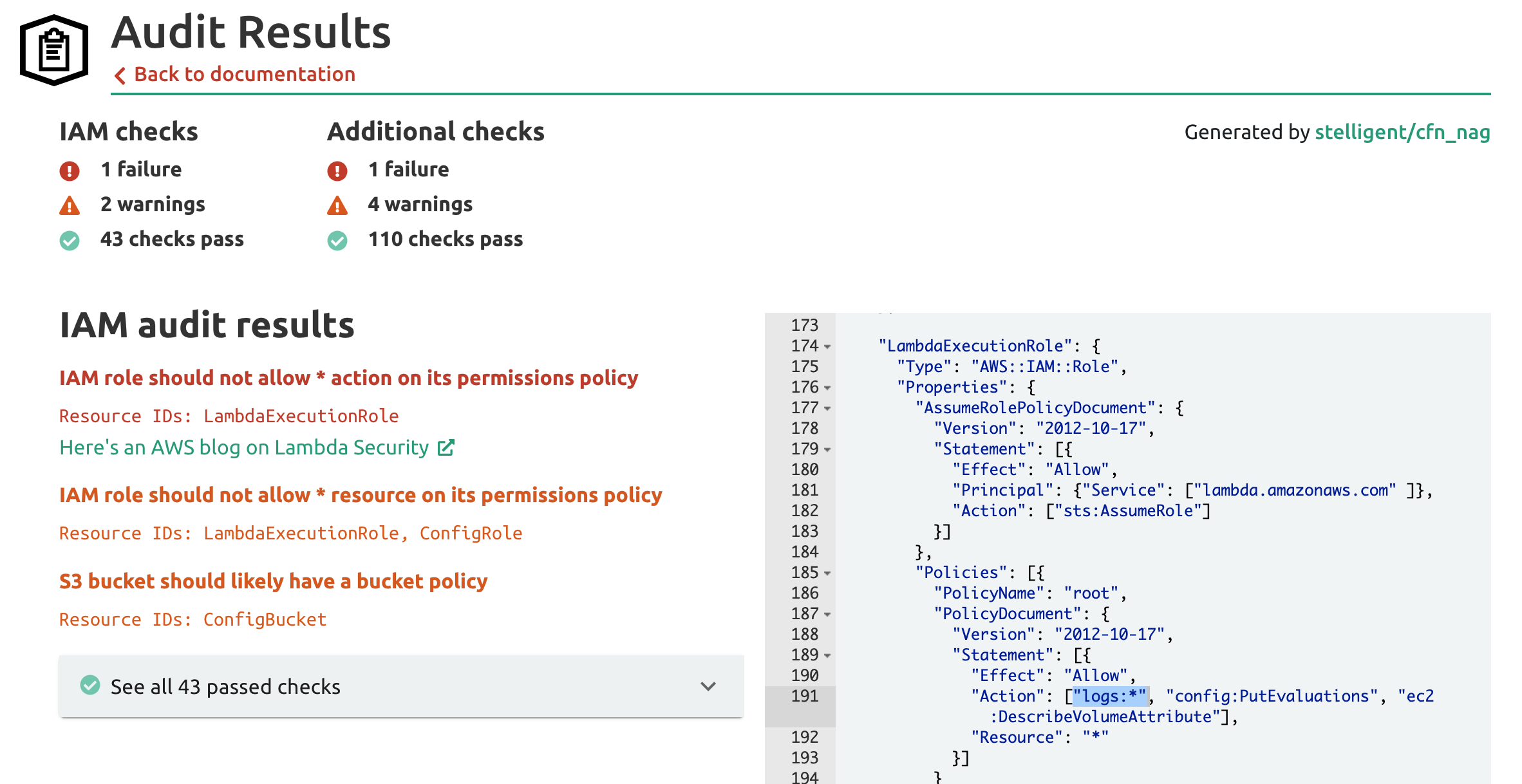
Unit 42 Cloud Threat Report: Misconfigured IAM Roles Lead to Thousands of Compromised Cloud Workloads










![アップデート]新IAM Policy Condition aws:CalledVia を学ぶ | DevelopersIO アップデート]新IAM Policy Condition aws:CalledVia を学ぶ | DevelopersIO](https://cdn-ssl-devio-img.classmethod.jp/wp-content/uploads/2020/02/2_07_46.png)